What Is Perimeter Security? (A Complete, Practical Guide)
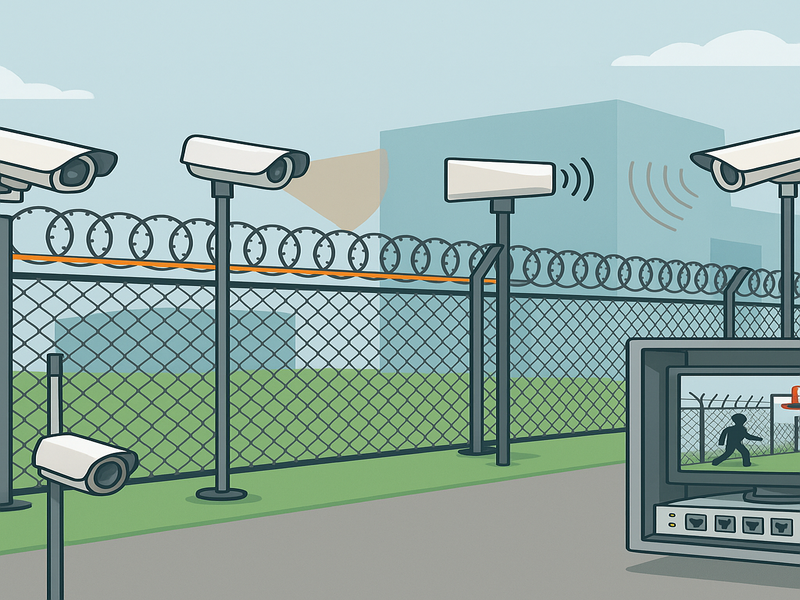
Perimeter security is the practice of protecting the outer boundary of a site so that threats are deterred, detected, delayed, and responded to before they affect people, assets, or operations. It blends physical barriers, sensing technologies, communications, trained personnel, and procedures into a layered system tailored to the risks of industrial plants, data centers, logistics hubs, utilities, airports, campuses, and other commercial environments. Done well, it reduces loss, downtime, and liability while enabling safe, efficient operations. Core Definitions & Concepts Perimeter vs. boundary vs. secure zone. The perimeter is the outermost boundary of control—often a fence line, property line, or virtual geofence on water or air approaches. Inside it, sites usually define zones: public, controlled, restricted, and critical. Each inner zone increases scrutiny and controls. The Deter–Detect–Delay–Respond–Recover model. Deter with signage, lighting, fencing, and visible patrols. Detect with sensors, cameras, analytics, and alarms. Delay using barriers, locks, sally ports, and distance. Respond via guards, first responders, and automated workflows. Recover by restoring service, preserving evidence, and learning from incidents. Defense-in-depth. No single sensor or barrier is perfect. Layering independent measures lowers the chance of a single point of failure and helps filter false and nuisance alarms. CPTED (Crime Prevention Through Environmental Design). Sightlines, landscaping, lighting uniformity, and controlled access points reduce concealment and opportunities for intrusion. Threat Landscape Threat actors: opportunistic thieves, organized crime, activist groups, disgruntled insiders, and curious trespassers. Tactics: cutting/climbing fences, tailgating vehicles, ramming gates, tampering with sensors, approaching by water, tunneling, drone overflights, and credential misuse. Environmental/operational hazards: wildlife, wind-blown debris, heavy rain/fog, RF interference, and construction works on or near the fence line. Risk framing: Combine likelihood (how often a tactic occurs) and impact (safety, financial loss, operational downtime, regulatory exposure). Focus investment where the product of likelihood × impact is highest. Perimeter Types & Use Cases Open perimeters: corporate campuses, parks. Emphasis on subtle deterrence, lighting, and video analytics. Fenced/controlled perimeters: manufacturing plants, warehouses. Typical mix of fencing, gates, ALPR, visitor controls, and multi-sensor detection. High-security sites: data centers, utilities, ports/airports. Dual fences with sterile zones, thermal/radar coverage, rigorous access control, and strict logging. Special perimeters: waterfronts, roofs, rail sidings, tunnels, and temporary/event perimeters requiring portable barriers and wireless sensing. Design Methodology (End-to-End) Define assets, threats, and risk tolerance. Map what you’re protecting and what failure looks like. Zoning & segmentation. Plan concentric layers and sterile zones between fences. Site survey. Terrain/soil conditions, drainage, line-of-sight, light levels, RF/EMI noise, prevailing winds, vegetation, and wildlife patterns. Requirements & metrics. Set target probability of detection (Pd), false alarm rate (FAR), nuisance alarm rate (NAR), availability, privacy, and safety expectations. Architecture selection. Choose barriers, sensors, communications, power, and C2 (command-and-control) platform. Validation & acceptance. Define test scripts (factory/site), performance acceptance criteria, documentation, and training deliverables. Physical Layer Components Barriers: anti-cut/anti-climb mesh, welded panels, T-walls, berms/ditches. Specify height, mesh aperture, topping (e.g., outriggers), and foundations suited to soil type and frost lines. Vehicle mitigation: fixed or retractable bollards, wedge barriers, crash-rated gates, and sally ports with interlocks. Portals & locks: doors/turnstiles (optical and full-height), locks (fail-safe vs. fail-secure), anti-passback policies. Lighting: uniformity ratio and vertical illumination matter more than raw lumens. Avoid glare and light trespass; consider dark-sky compliance while ensuring camera performance. Detection & Sensing Technologies Fence-mounted sensors: microphonic/accelerometer cables and fiber-optic sensing detect cut/climb events on the fence fabric. Ground/buried sensors: seismic, magnetic, pressure, and leaky coax systems form invisible trip lines along the boundary. Volumetric sensors: active infrared beams, microwave, radar, LiDAR, and PIR arrays cover areas between the fence and buildings. Video surveillance: fixed, PTZ, thermal, and multispectral cameras; analytics for line-crossing, loitering, person/vehicle classification. Electrified fencing: adds strong deterrence and detection (alarm on cut/short). Apply strict electrical safety and signage. Intercoms & call points: give people a way to request help without breaching the perimeter. Quick comparison (illustrative): Technology Typical Use Coverage Strengths Limitations Fence-mounted cable Fence lines Linear, continuous Localizes cut/climb, discreet Sensitive to loose panels/vegetation Fiber-optic fence High-security fences Long runs, zoneable EMI-immune, precise localization Higher CapEx, skilled tuning Buried sensor Invisible trip lines Linear zones Covert, weather-agnostic Complex civil works; soil-dependent Microwave Sterile zones Wide volumetric Strong in fog/dust, long range Multipath near metal Active IR beams Gate lines/roofs Beam paths Sharp trip lines Fog/snow occlusion Radar Wide-area Fan volumes Tracks moving objects Costs/false returns in clutter Thermal cameras Long perimeters Line-of-sight Works in darkness, detects humans Cost; needs analytics Visible cameras + analytics General LoS & zones Evidence + verification Lighting & shadows Privacy, Ethics & Legal Be transparent: signage at entries, purpose limitation for data use, and retention policies appropriate to risk. Mask private spaces, enable privacy zones in cameras, and consider privacy impact assessments for analytics and biometrics. Balance deterrence with user experience—especially on mixed-use campuses and public-facing sites. Environmental & Site Challenges Design for temperature extremes, icing, salt fog, dust/sand, and corrosive atmospheres. Select enclosures and finishes accordingly (e.g., stainless hardware, powder-coated or hot-dip galvanized steel). Mitigate vegetation (scheduled trimming), terrain masking (elevated poles, overlapping coverage), RF interference (spectrum planning), and lightning (bonding/grounding, surge protection). Procurement & Budgeting Model TCO across 5–10 years: CapEx (civil works, hardware, software licenses) and OpEx (monitoring, maintenance, spares, connectivity). Phase deployments: start with high-risk segments and quick wins (lighting, analytics), then expand. In RFPs, specify performance metrics, environmental test cases, cybersecurity hardening requirements, training hours, and support SLAs—not just parts lists. Installation & Commissioning Coordinate civil works (trenching, footings) with cable paths and drainage. Document device placement and run calibration (e.g., fence sensor tension, radar zones, camera FOVs with height charts). Execute acceptance scripts: walk-tests at set intervals, vehicle approaches at gates, alarm workflows from sensor through operator acknowledgment to dispatch logging. Capture as-built drawings and a complete asset register with firmware versions. Maintenance & Lifecycle Adopt a preventive maintenance schedule: fence torque checks, camera cleaning, desiccant replacement, heater verification, re-aiming after storms, sensor recalibration, and vegetation control. Maintain firmware lifecycles, backups, and vulnerability scans. Plan for end-of-life hardware and feature updates; avoid single-vendor lock-in where possible. Vertical-Specific Design Notes Utilities